When Extensibility Creates Leverage (and When It Creates Liability)
A practical decision framework for SaaS product leaders and platform operators: when does extensibility create real leverage versus liability, and what should you open up first—and what should you keep locked down? Includes step-by-step evaluation process and readiness checklist.
When Extensibility Creates Leverage (and When It Creates Liability)
Extensibility is one of those words that sounds universally good.
“Open up the platform.” “Let developers build.” “Launch a marketplace.”
Sometimes that turns a product into a compounding machine.
Other times it turns your roadmap into a negotiation, your security posture into a dice roll, and your customers into unpaid QA.
This post is a practical decision framework for SaaS product leaders and platform operators:
- When does extensibility create real leverage?
- When does it create liability?
- What should you open up first—and what should you keep locked down?
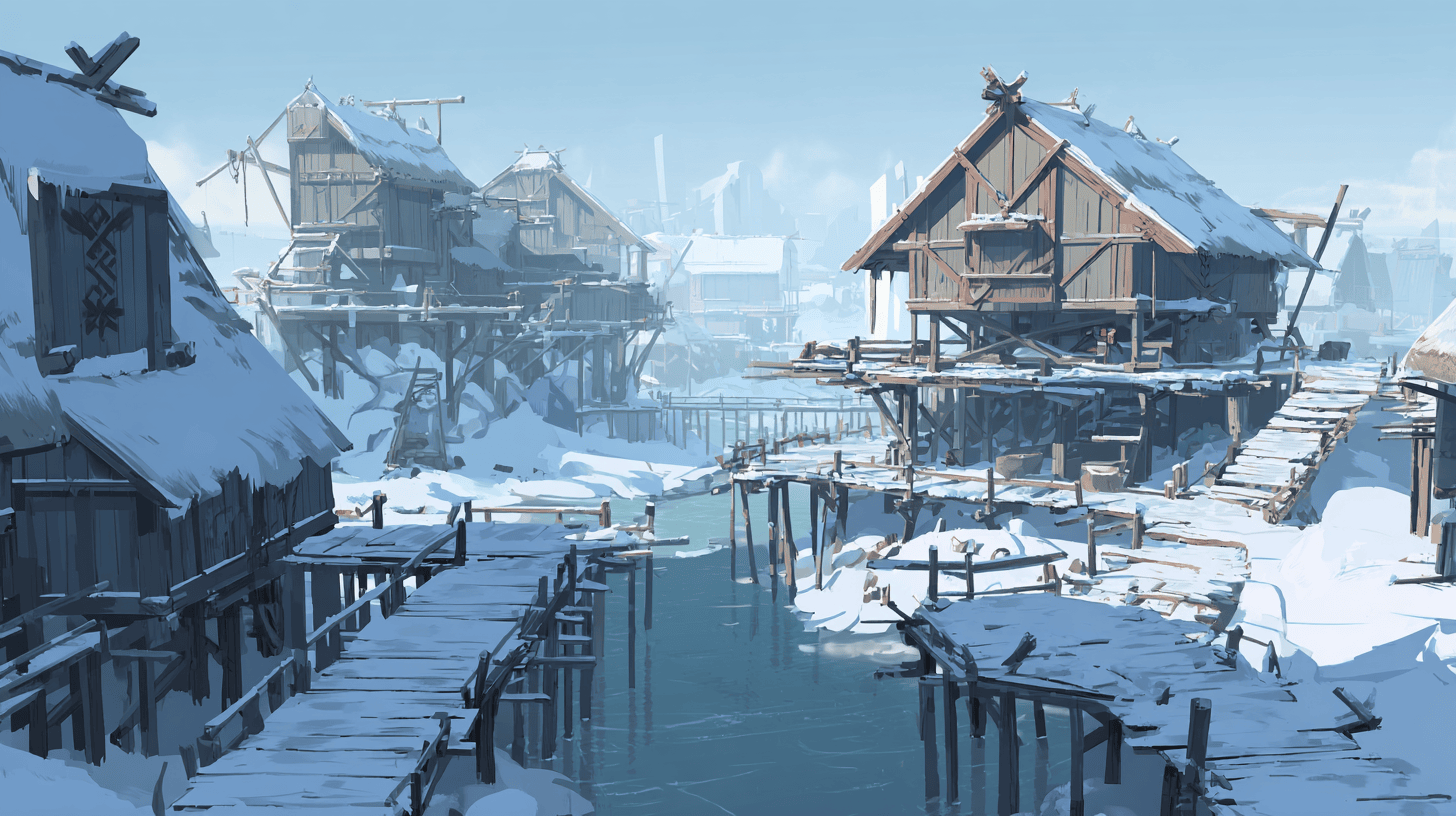
Think of it like building a Viking village.
A village thrives when outsiders can set up shops and add value within the rules of the settlement—on solid foundations, with guardrails that prevent fires from spreading. A village collapses when anyone can build anything anywhere, wire it into your water supply, and call it “innovation.”
Extensibility isn’t a feature. It’s a business model.
The moment you support third-party extensions, you’re no longer shipping “just a product.”
You’re shipping:
- A runtime (where code executes)
- An interface contract (APIs, events, UI extension points)
- A trust system (permissions, reviews, enforcement)
- A market (discovery, distribution, monetisation)
That can be an enormous advantage—if you treat it like a first-class product.
The 3 levers: how extensibility creates leverage
1) Coverage: the long tail becomes addressable
No internal team can ship every niche workflow.
Extensibility lets you serve the long tail without bloating the core product. Your platform stays focused; the ecosystem handles variation.
Signal it’s working: customers stop saying “Does it support X?” and start saying “Which app should I use for X?”
2) Speed: parallel innovation beats roadmap gravity
A healthy ecosystem increases feature velocity without increasing headcount.
Partners build new capabilities in parallel—often faster than you can, especially in specialized domains.
Signal it’s working: high-quality apps appear for emerging needs before they show up on your core roadmap.
3) Network effects: value compounds with each new builder
Every useful extension can increase platform value for all users. That attracts more users, which attracts more builders, which creates more value.
It’s the flywheel everyone wants.
Signal it’s working: your best growth channel starts looking like “ecosystem referrals” rather than paid acquisition.
The 3 liabilities: how extensibility creates risk
1) Security: your attack surface expands overnight
If third-party code can touch customer data, you’ve multiplied the number of ways things can go wrong.
Even with good intentions, many extensions will ship with flaws.
Signal it’s failing: security incidents are increasingly “someone else’s code” but still “your problem.”
2) Complexity: you inherit ecosystem debt
Every extension point becomes a contract. Every contract becomes a constraint.
If you don’t version and govern these contracts, you’ll end up afraid to change anything because “it might break partners.”
Signal it’s failing: core product decisions are delayed because “we need to check with the ecosystem.”
3) Trust: customers blame you, not the plugin
From the customer’s perspective, the platform is one experience.
When an app breaks, harms performance, or creates bad outcomes—users rarely say “that vendor messed up.” They say, “Your platform is unreliable.”
Signal it’s failing: support load grows faster than user growth, and the stories include “we installed an app and everything went sideways.”
A decision framework: should you open this up?
Use this quick test before building “a marketplace” as a default move.
Step 1: Identify what kind of extensibility you actually need
Not all extensibility is the same. Common categories:
- Integrations: connect to external tools (data in/out)
- Automations: triggers/actions, workflow orchestration
- UI extensions: embed panels, widgets, surfaces in your app
- Data extensions: custom objects, schemas, calculated fields
- Compute extensions: custom logic that runs near/inside your platform
Most SaaS companies should start with integrations + automations before jumping to “arbitrary code execution.”
Step 2: Score the upside (Leverage)
Rate each proposed extension area 1–5:
- Long-tail coverage: does this unlock many niche workflows?
- Partner innovation: are there capable builders ready to ship value?
- Network effect potential: will successful apps attract more users/builders?
If it’s mostly “nice-to-have integrations,” you may not need a marketplace yet—you may just need a good integration layer.
Step 3: Score the downside (Liability)
Rate 1–5:
- Data sensitivity: will plugins touch regulated or high-risk data?
- Core coupling: will this constrain your roadmap and architecture?
- Blast radius: if an extension fails, can it degrade the whole system?
If blast radius is high and isolation is weak, pause. That’s not a “marketplace problem.” That’s an architecture problem.
Step 4: Decide your initial “safest” extension surface
A good early extensibility surface has:
- Clear user value
- Limited permissions
- Strong isolation
- Easy testability
For most platforms, the safest first move looks like:
- Webhooks + API
- Automations (trigger/action)
- UI embed surfaces (iframe-like)
- Managed runtime / serverless functions
- Deep in-product plugins (high power, high risk)
The “middle path” principle: constrained power beats total freedom
There’s a myth that the best platforms are the most flexible.
In practice, the best platforms are the ones that provide power inside constraints:
- Plugins can do meaningful work…
- …without full access to everything…
- …and without being able to take down the host.
This is why many modern platforms converge on patterns like:
- Permission scopes
- Sandboxed runtimes
- Capability-based APIs
- Rate limits + quotas
- Review gates + trust tiers
The goal is simple:
Make it easy to extend the platform in ways that are safe by default.
What to open first: a practical sequence
If you’re early (or rebuilding), this sequencing tends to work:
Phase 1: Integration platform
- Clean REST/GraphQL APIs
- OAuth & scopes
- Webhooks/event stream
- Great docs + quickstarts
- Example integrations for common tools
Win condition: developers can reliably connect systems without begging your team.
Phase 2: Workflow and automation layer
- Triggers/actions
- Idempotency patterns
- Observability (logs, retries, dead-letter)
- Minimal UI configuration surfaces
Win condition: non-developers can stitch workflows; devs can build powerful automations safely.
Phase 3: UI extension points
- Defined surfaces (panels, cards, modals)
- Strict performance budgets
- Isolation by default (embedded surfaces, message passing)
Win condition: ecosystem can shape user workflows without forking your UX.
Phase 4: Managed compute runtime (the “platform inside the platform”)
- Serverless functions / edge functions
- Data access via scoped APIs
- Strong sandboxing and egress controls
- Audit logs and permission prompts
Win condition: partners can ship real product logic without running their own infra—and you can keep trust intact.
Phase 5: Marketplace and monetisation (once discovery matters)
- Listings, ranking, reviews
- Billing, trials, refunds
- Fraud controls
- Governance & enforcement playbooks
Win condition: customers can reliably discover trusted solutions; developers can build sustainable businesses.
Common failure modes (and how to avoid them)
Failure mode 1: “We launched a marketplace before we had a platform”
If your APIs are brittle, docs are thin, and extension points aren’t stable, a marketplace amplifies pain.
Fix: invest in the platform foundations first. Treat developer experience like product experience.
Failure mode 2: “Anything can access everything”
This is the fastest route to security incidents and customer distrust.
Fix: introduce scopes, least privilege, sandboxing, and explicit permission prompts early.
Failure mode 3: “Partners became a veto group”
You can end up unable to evolve the product.
Fix: version APIs, publish deprecation policies, provide migration tooling, and avoid hidden breaking changes.
Failure mode 4: “Discoverability collapse”
At 50 apps, browsing works. At 500, search matters. At 5,000, curation matters.
Fix: build discovery as a product: categories, collections, trust badges, ranking signals, and anti-spam.
A simple readiness checklist
Before you “go full platform,” make sure you can answer yes to most of these:
- We have stable APIs and a public deprecation policy
- We can isolate extension execution (or we aren’t running third-party code yet)
- We have a permissions model (scopes) and audit logging
- We can monitor extension failures and rate-limit abuse
- We have a plan for review gates (even if lightweight at first)
- We know our monetisation model and the incentives it creates
- We have an owner/team for “ecosystem operations” (support, trust & safety, partner success)
If you’re missing several of these, extensibility may still be the right direction—but your next move should be platform foundations, not “marketplace launch.”
Forge’s POV: extensibility should feel safe by default
The future isn’t “every company becomes a marketplace.”
It’s that every serious SaaS product becomes more platform-shaped—because customers expect their tools to compose, integrate, and adapt.
The winners will be the teams that:
- Open up the right surfaces in the right sequence
- Invest in trust and governance as product capabilities
- Provide a stable, constrained runtime that partners can rely on
That’s what turns extensibility into leverage instead of liability.

